Configure the VPN concentrator to authorize users against Radius server. Test it and if everything works as it should add Notakey in between to provide second factor.
Create an VPN application in the Notakey authentication server if you don’t have it done already. More …
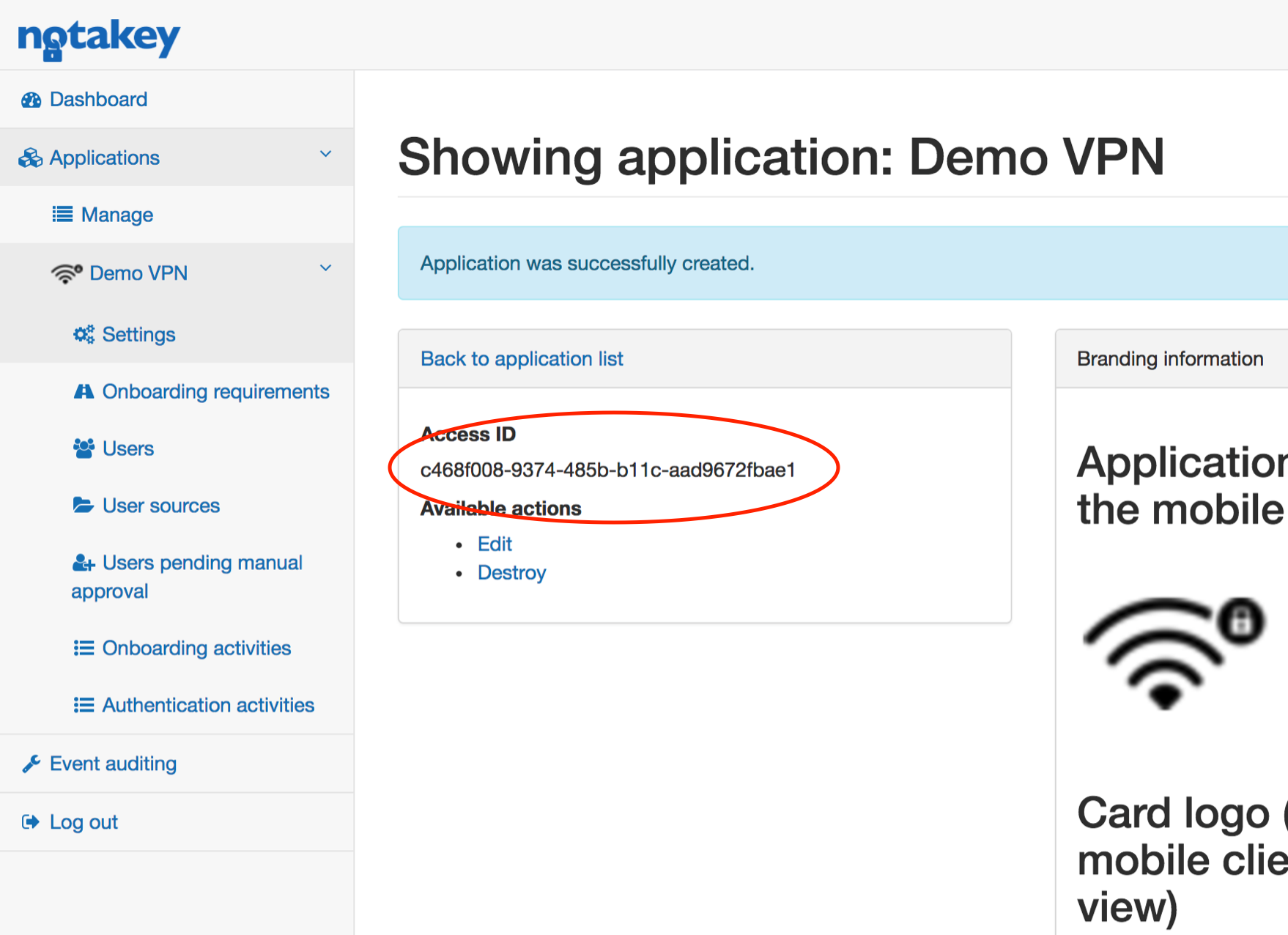
Copy access ID , you will need it later.
On-premise version setup
You have to configure built in auth-proxy service. Here you can find reference to all possible configuration settings: Authentication Proxy
Point your concentrator to NAA instead of Radius server.
Prepare configuration json, change “vpn_access_id” (Application access ID in the Notakey appliance dashboard, see picture above) and “vpn_radius_address” (Your real Radius server IP).
{
"vpn_port_in": "1812",
"vpn_port_out": "1812",
"vpn_radius_address": "10.0.1.23",
"vpn_secret_in": "secret_to_radius_server",
"vpn_secret_out": "secret_to_radius_server",
"vpn_access_id": "c468f008-485b-b11c-aad9672fbae1",
"vpn_message_ttl": "30",
"message_title": ""VPN authentication."",
"message_description": ""Allow {0} login?""
}
Feed configuration keys with command:
ntk cfg set :ap '{
"vpn_port_in": "1812",
"vpn_port_out": "1812",
"vpn_radius_address": "10.0.1.23",
"vpn_secret_in": "secret_to_radius_server",
"vpn_secret_out": "secret_to_radius_server",
"vpn_access_id": "c468f008-485b-b11c-aad9672fbae1",
"vpn_message_ttl": "30",
"message_title": ""VPN authentication."",
"message_description": ""Allow {0} login?""
}' --json-input
and restart auth-proxy:
ntk ap restart
We are using “:” before the ap key, so this setup is stored globally in the cluster. If you have many VM you just need to restart ap service on each of them.
User name should be the same in the Notakay appliance and in the Radius
Cloud version setup
You have to use dockerized auth-proxy service in your local network as a proxy to the radius server. Communication in between auth-proxy and Notakey appliance is encrypted and safe to be used outside LAN. Example:
docker run --name auth-proxy \
-e NOTAKEY_HOST="https://2fa.your_company.com/api" \
-e NOTAKEY_ACCESS_ID="c468f008-485b-b11c-aad9672fbae1" \
-p 1812:1812/udp \
-e LISTEN_ADDRESS=0.0.0.0 \
-e ADDRESS_SECRET_IN=0.0.0.0:secret_to_radius_server \
-e DOWNSTREAM_ADDRESS=10.0.1.23 \
-e SECRET_OUT=secret_to_radius_server \
notakey/authproxy:latest

